
Cybercrimes have become an increasingly prevalent form of misdeed, affecting people the world over in seemingly small spans of time. Most people are familiar now with the different types of online scams you might encounter, both through email and through text messages. However, some hackers pick bigger fish to fry, targeting major multinational corporations, various service providers, and even entire countries.
Striking with precision through these massive conglomerates and networks, crypto-criminals have stolen the data of billions of consumers and used their internet prowess to instill fear, send subtle messages, and shut down entire systems from within. These attacks also resulted in stronger and stricter data protection laws worldwide. Though one cannot help but be amazed by the hacking skills of these smooth operators, it is a truly daunting notion to think that each of us has likely had our data stolen in one of these infamously destructive super-hacks that shocked the world.

(By Mike Mozart, Wikimedia Commons)
One of the earliest victims of a mass cyber-attack was none other than the banking subsidiary of the well known multinational financial corporation, Citigroup. Citibank itself has over 2500 branches in 19 different countries across the globe.
In 1994, a Russian man named Vladimir Leonidovich Levin purportedly masterminded an illicit online transfer of over $10 million from Citibank servers. Using the internal dial-up wire transfer service of the company, he, along with a number of accomplices, gained access to the accounts of some Citibank corporate customers and sent the funds to accounts set up in various countries.
His accomplices were arrested later that year while attempting to access their illegal bounty, and Levin was arrested in London in 1995, before being extradited to the U.S. for trial. He admitted to defrauding the bank and stealing $3.7 million. His sentence was 3 years in jail and he was ordered to make financial restitution. Citibank claims that all but $400,000 out of the total money stolen was recovered.

(By Dirk Ingo Franke, Wikimedia Commons)
In 2008, the supermarket and pharmacy chain Hannaford Brothers Co. fell victim to a series of hacks committed by a group of three. By infiltrating the Heartland Payment System, they were able to access the credit and debit card data of customers of certain franchises, like 7-Eleven.
Hannaford was among the biggest companies hit by this target-specific group. The investigation discovered that the conspirators uploaded malware onto the servers of Hannaford which allowed them to steal card numbers and expiration dates, data stored specifically on the magnetic strip on every card, though not the customers' names.
Despite Hannaford adhering to the Payment Card Industry Rules in place at the time, the hackers successfully attacked the data of 300 different stores, stealing the data of 4.2 million customers and leading to nearly 2000 cases of fraud.

The Sony Corporation, a multinational conglomerate based out of Japan, is one of the largest producers of electronics in the world. Their products include everything from phones and appliances to video game consoles like the PlayStation, which experienced a global network shut down in 2011.
Between April 17th and 19th, 2011, the PlayStation Network (PSN) and Sony Entertainment Network were attacked by a security hacker, exposing the personal data of users worldwide. During the two-day attack, users were shut out of their accounts as their data was stolen, and Sony was forced to shut down the entire PSN as they attempted to eliminate the security breach. A week or so prior to the network being turned back on, a firmware was released by the company as a security patch for the software.
The network outage continued for a massive 23 days (which was likely a nightmare for PS users and a dream for their parents). However, the attack resulted in the data of 77 million registered PSN account-holders being stolen. Though no incidents of credit card fraud related to the breach were officially reported, Sony received much criticism for its handling of the attack.

(By Kalra.geet25, Wikimedia Commons)
Just prior to Sony’s network outage, a subsidiary of the Alliance Data Systems Corporation that specializes in digital marketing and IT solutions called Epsilon was struck by a tsunami of its own. At the time, Epsilon was the email service provider for over 2500 major companies.
Despite being warned that possible network security breaches were on the rise in 2011, Epsilon still found itself exposed to the sticky fingers of cyber bandits. The email addresses of customers for 50 different companies were stolen, including but not limited to JPMorgan Chase, Citigroup, Best Buy, Disney Destinations, and TiVo.
Though Epsilon never released an official list of companies affected, the above-mentioned companies and many others released statements to customers shortly after Epsilon was alerted of the breach, advising them to be cautious of any marketing emails opened and attachments downloaded as they may be phishing emails, which are far more likely to be opened when sent from an authorized and expected source.

Yet another target of a group of sophisticated cyber-criminals was the professional and social networking website, LinkedIn. In 2012, they were struck with a single explosive attack that resulted in the theft of 6.5 million users passwords. The company responded immediately by completely restricting access to the accounts of all hacked users.
The company also stated that they would be emailing all affected users with security and password reset instructions. However, this data breach opened eyes to the sheer volume of personal data submitted to major online corporations, as well as the access to other accounts that cyber-criminals can gain through a single password.
A lawsuit was filed on behalf of all affected LinkedIn users, resulting in compensation, restitution, and injunctive action to strengthen security protocols. In 2016, an arrest was made in connection to this attack, and further investigation revealed an additional 100 million users hacked. All members of LinkedIn that had not reset their passwords since 2012 were required to do so.

(By gaku, Wikimedia Commons)
One of the most well-known companies in the world that is regarded to be a pioneer of early internet-era services, Yahoo! was the victim of not one, but two separate information and data thefts in 2013 and then in 2014. Both breaches stand among the largest data hacks ever committed.
In September 2016, the company announced that a breach occurred in 2014 that made use of web cookies designed to replace login credentials with false information in order to gain access to the accounts of 500 million users. It was only in December 2016, that the details of the 2013 breach were also revealed to the public.
Initially, the company estimated that 1 billion users had been affected by the breaches. However, it was later confirmed in 2017 that all 3 billion Yahoo! users had been affected by both the attacks. Data stolen included names, addresses, contact numbers, passwords, security questions, and answers.

(By Kgbo, Wikimedia Commons)
While Yahoo! was watching history unfold before them in 2014, the largest bank in America, and 7th largest in the world, JPMorgan Chase was falling prey to a different group of cyber-sleuths, a group that also attacked numerous other major financial groups at the same time frame, including HSBC Holdings and Citigroup.
In what has since been described as the largest financial related information breach, the information of 76 million households, a total of 83 million account-holders, as well as 7 million small businesses was retrieved by hackers. Even though login information was not compromised, names, email IDs, phone numbers and addresses were, exposing all affected customers to possible phishing attacks.
In 2015, 4 hackers were indicted by the US government, one of whom was an American. Two were arrested in Israel and extradition was requested. Though information was stolen leading to numerous concerns of fraud, no actual money was stolen.
(By Jbuket, Wikimedia Commons)
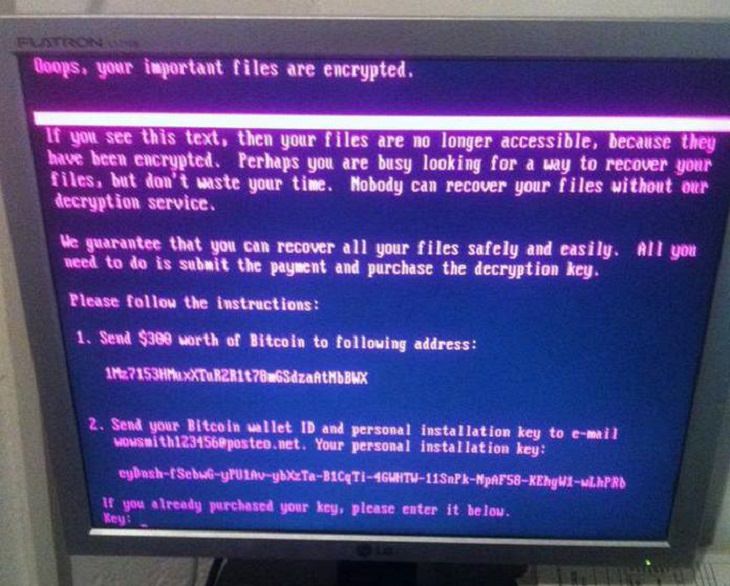
Petya, also known as Balogh, is not a company but the name of a family of malware that was first discovered in 2016 that specifically targets systems using Microsoft Windows. There were 2 separate attacks with this malware, each affecting millions of people through email attachments.
Once downloaded onto a system, it infects one of the main storage components and encrypts the user's hard drive and then stops the system from rebooting. For users to regain access to their drives and reboot their systems, the malware first demands a payment to be made in Bitcoin, essentially holding users' hard drives ransom.
The 2nd attack occurred in 2017 with an updated version of the virus called NotPetya. The second attack was more targeted, striking various Ukrainian companies and organizations. Experts believed that this attack was largely politically motivated. The maker of the original Petya virus was eventually apprehended.

Just a month before Ukraine was struck by NotPetya, the entire globe was hit with another ransomware attack that was Microsoft Windows-specific. Much like Petya, this malware would encrypt the user’s data and consequently demand a Bitcoin payment for its release.
It was developed from an NSA (National Security Agency) software called EternalBlue, which was stolen and leaked prior to the attack by the Shadow Brokers. WannaCry struck 200,000 users in nearly 150 different countries and exploited Windows users into paying millions of dollars.
The attack mercifully only lasted a few days, as Microsoft released emergency patches within a short period of time to analyze the virus. A killswitch was discovered which prevented the worm from infecting any more computers. Many countries have since asserted a belief that North Korea was responsible for WannaCry.
Share this article with family and friends!